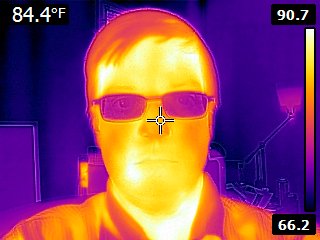
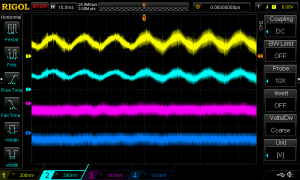
Last night I went to a lecture series hosted by the Janelia Farm Research Campus of the Howard Hughes Medical Institute. The talk, on the evolution of human color vision, was terrific—and I was given the opportunity to take a tour of their lab facilities.
(Click the image above for a small gallery of additional pictures).